Meet A.L.I.C.E.: The mobile game that teaches you about cyber security
You’re a first year UNSW student. It’s O Week, and you’ve registered with so many societies and courses and programs that you barely remember even the simplest of passwords. But who cares? What’s a couple of weak passwords when there’s a pub crawl to be getting to.
Not so fast. That one weak password (let’s face it, you’ve been using Dog123 for everything) has come back to haunt you. And now someone has stolen your identity.
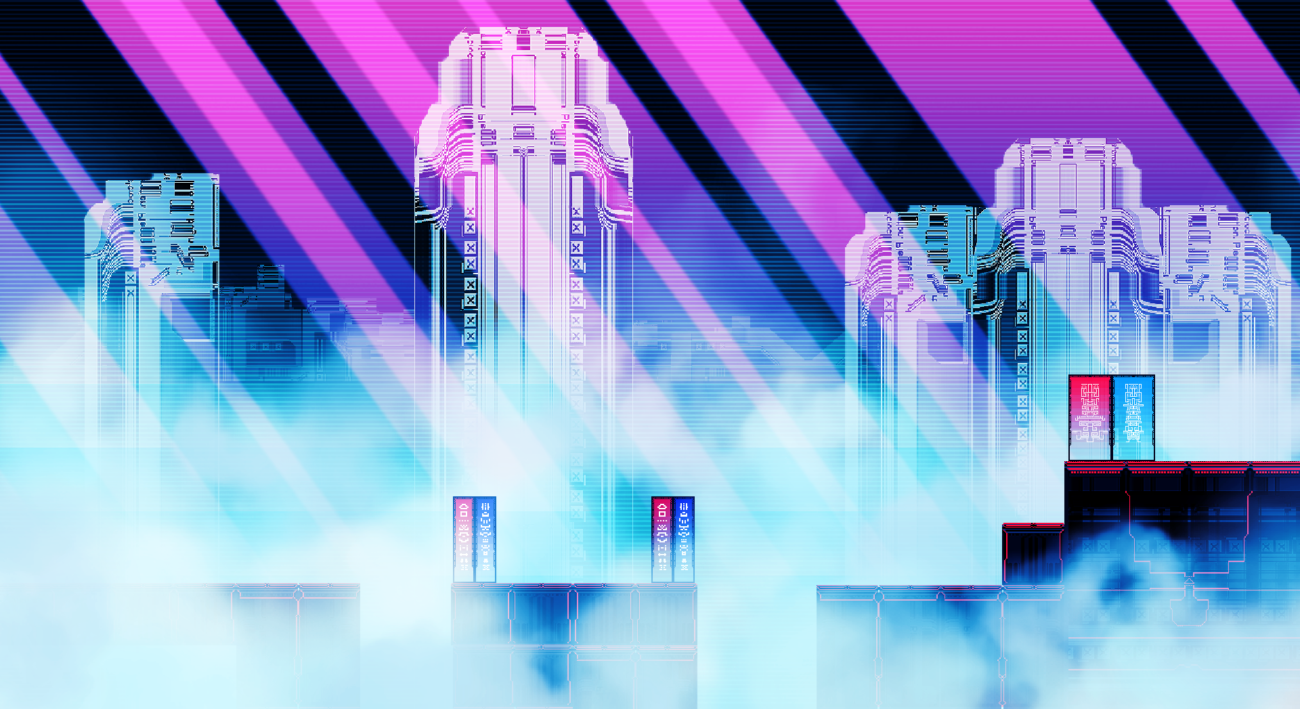
To reclaim it, you’ll need to find a way into and through the university’s digital network. Lucky for you, an assistive A.I. called A.L.I.C.E. offers her assistance. With her help you’ll be able to navigate the different levels of the network, bypassing its security and avoiding the attacks of each and every cyber threat that comes your way. But not everything in this digital world is as it seems…

A short biography
Created by an ace team including some of our own and the guys over at UNSW, A.L.I.C.E. is a mobile game designed to teach university students – and anyone else – about cyber security. Playable in roughly 20 minutes, the game invites you on a quest through the twists and turns of a digital world as you race to recover your stolen identity. As you make your way through the network, you’ll need use your wits to outsmart evil viruses, beat vicious malware, and ward off phishing attacks, all with the help of your trusty A.I. assistant, A.L.I.C.E.

A.L.I.C.E. launched during UNSW O Week 2018, and is now available on both iOS and Android. Do yourself a favour and download the mobile game to learn a little bit more about the threats that await you every time you log online.
In the meantime, let’s take a look at the things you’ll learn if you play…
Passwords, passwords, passwords
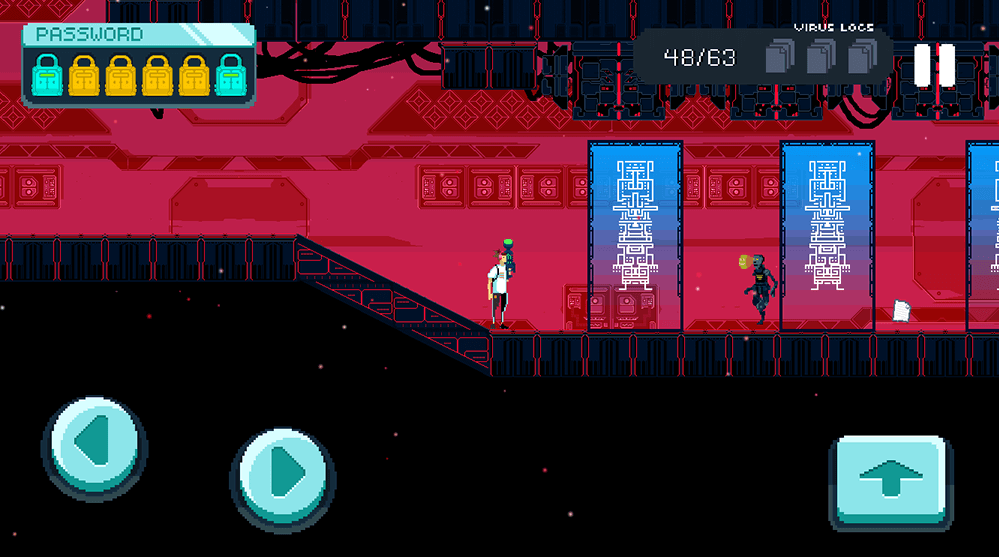
Passwords are a crucial part of the game, just as they are a crucial part of effective cyber security. At the beginning of A.L.I.C.E., you’ll be asked to set a password. The strength (or weakness) of this password will determine your health for the rest of the game. Every time you’re hit by a virus, your password protection will be compromised, revealing a letter (or more) for anyone to see. And if your whole password is guessed? Well that’s game over folks.

Brute force-ing your way
Ever wondered why passwords like Dog123 are so bad? Spoiler: It’s not because some person might guess it at random. The real threat to weak passwords are computers that run through millions of combinations to easily crack thousands of passwords in one go, including yours. In the game, if you’re hit by one of these brute force attacks, your password health bar will start running like a poker machine to guess parts of your password. The weaker the password, the easier it will be for these kinds of attacks to succeed.

Attack of the viruses
If you’re to make it to through the mobile game, you’ll need to avoid or defeat the viruses and worms that run rampant across the network. To do so, you’ll have to capture and collect the critters and send them back behind the firewall. Whenever you manage to catch a virus, it will also be added to your virus log, where you can discover more information about its unique purpose and characteristics. After all, who knows what kind of information might come in handy.

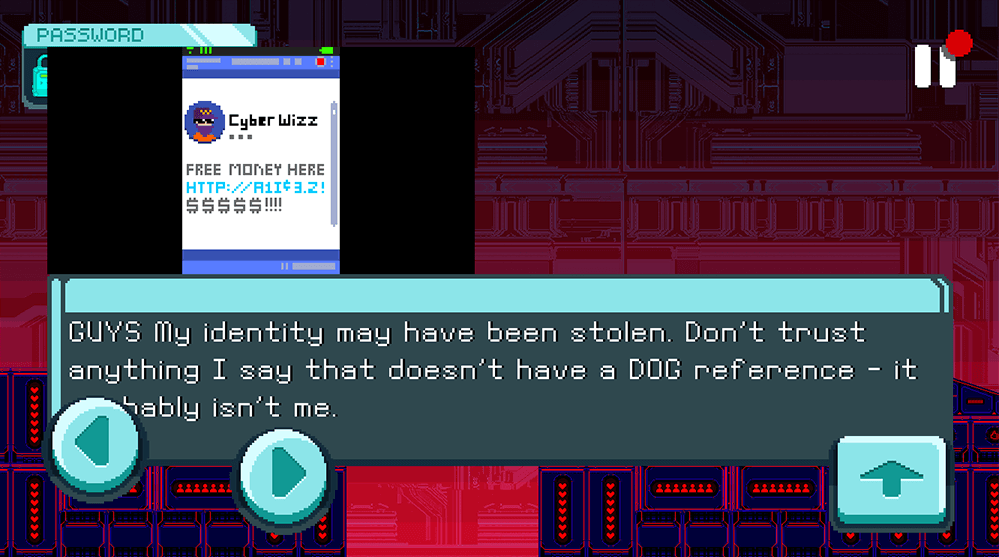
Phishing for new identities
As you move through the mobile game, you’ll be confronted by a series of correspondence. But there’s something phishy here. While some of these emails are legitimate, others are designed to lure you in and steal your personal information – a tactic called, you guessed it, phishing. Finding your stolen identity will require you to figure out what’s real and what’s fake. You’ll also need to avoid the phishing bots that are behind these emails, because they too are lurking throughout the network, waiting for you to let your guard down.
Social engineering information
The more information that people collect about you online, the more they’ll be able to use it against you. You’ll need to be careful as you move through the network, because any information you divulge could be a threat to your cyber security in the future. But remember, social engineering can work for you as well as against you. Information is abundant in this digital world, so keep your wits about you and you may uncover sensitive information about the network and its inhabitants that can help you to succeed.
Ready, set… play!
If all of this sounds pretty rad, that’s probably because it is. It’s also probably a sign that you should head to one of the links below and download A.L.I.C.E. for yourself.

A.L.I.C.E. Cyber Security Game
Retro-inspired mobile game educates about cyber security.







